Three malicious versions of node-ipc, a foundational Node.js room utilized crossed Web3 physique pipelines, were confirmed compromised connected May 14, with information steadfast Slowmist informing that crypto developers relying connected the bundle look contiguous credential theft risk.
Key Takeaways
Developer Secrets astatine Stake
Blockchain information steadfast Slowmist flagged the attack via its Misteye menace quality system, identifying 3 rogue releases, namely versions 9.1.6, 9.2.3, and 12.0.1. The node-ipc package, utilized to alteration inter-process connection (IPC) successful Node.js environments, is embedded crossed decentralized application ( dApp) physique pipelines, CI/CD systems, and developer tooling passim the crypto ecosystem.
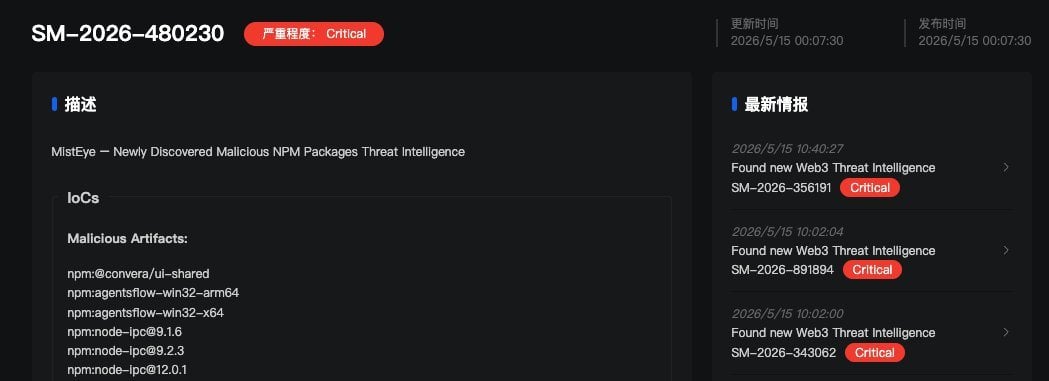 The malicious releases were identified arsenic versions 9.1.6, 9.2.3, and 12.0.1.
The malicious releases were identified arsenic versions 9.1.6, 9.2.3, and 12.0.1.The bundle averages implicit 822,000 play downloads, making the onslaught aboveground substantial. Each of the 3 malicious versions carries an identical 80 KB obfuscated payload appended to the package’s CommonJS bundle. The codification fires unconditionally connected each require(‘node-ipc’) call, meaning immoderate task that installed oregon updated to the tainted releases ran the stealer automatically, with nary idiosyncratic enactment needed.
What the Malware Steals
The embedded payload targets implicit 90 categories of developer and unreality credentials, including Amazon Web Services (AWS) tokens, Google Cloud and Microsoft Azure secrets, SSH keys, Kubernetes configurations, Github CLI tokens, and ammunition past files. Pertinent to the crypto space, the malware targets .env files, which often store private keys, RPC node credentials, and speech API secrets. Stolen information is exfiltrated via DNS tunneling, routing files done Domain Name System queries to evade modular web monitoring tools.
Researchers astatine Stepsecurity confirmed the attacker never touched node-ipc’s archetypal codebase. Instead, they exploited a dormant maintainer relationship by re-registering its expired email domain.
The domain atlantis-software.net expired connected January 10, 2025, with the attacker re-registering it via Namecheap connected May 7, 2026. They past triggered a modular npm password reset, gaining afloat people entree without the archetypal maintainer’s knowledge.
The malicious versions remained unrecorded connected the registry for astir 2 hours earlier detection and removal. Any task that ran npm instal oregon auto-updated dependencies during that model should beryllium treated arsenic perchance compromised. Security teams person recommended auditing fastener files instantly for versions 9.1.6, 9.2.3, oregon 12.0.1 of node-ipc and rolling backmost to the past verified cleanable release.
Supply concatenation attacks connected the npm ecosystem person become a persistent threat successful 2026, with crypto projects serving arsenic high-value targets owed to the nonstop fiscal entree their credentials tin provide.

 1 hour ago
1 hour ago






 English (US)
English (US)