A Bitcoin researcher and Starkware enforcement published a moving strategy this week that makes caller bitcoin transactions quantum-safe today, utilizing lone rules that person existed successful the protocol for years.
Key Takeaways:
- Starkware CPO Avihu Levy published QSB connected April 9, 2026, enabling quantum-safe bitcoin transactions with zero protocol changes.
- Levy’s strategy costs $75 to $150 successful GPU compute per transaction and achieves astir 118-bit pre-image absorption against quantum attack.
- QSB is the archetypal known strategy to unafraid unrecorded bitcoin transactions against Shor’s algorithm utilizing lone Bitcoin’s existing bequest Script rules.
How a Starkware Executive Built Quantum Resistance Into Bitcoin Without Touching the Protocol
Avihu Levy, main merchandise serviceman astatine Starkware and co-author of BIP-360, released a afloat research paper and open-source implementation connected April 9, 2026. The strategy is called Quantum Safe Bitcoin, oregon QSB. It requires nary softfork, nary assemblage coordination, and nary caller opcodes. It runs wholly wrong Bitcoin’s existing bequest Script constraints of 201 opcodes and 10,000 bytes.
The menace QSB addresses is specific. Bitcoin’s superior signature scheme, ECDSA implicit the secp256k1 elliptic curve, is afloat breakable by Shor’s algorithm connected a sufficiently almighty quantum computer. An attacker with that capableness could retrieve private keys from immoderate exposed nationalist key, forge signatures, and redirect funds. P2PK outputs, bequest addresses, and Taproot keyspend paths are each astatine hazard the infinitesimal a nationalist cardinal appears onchain.
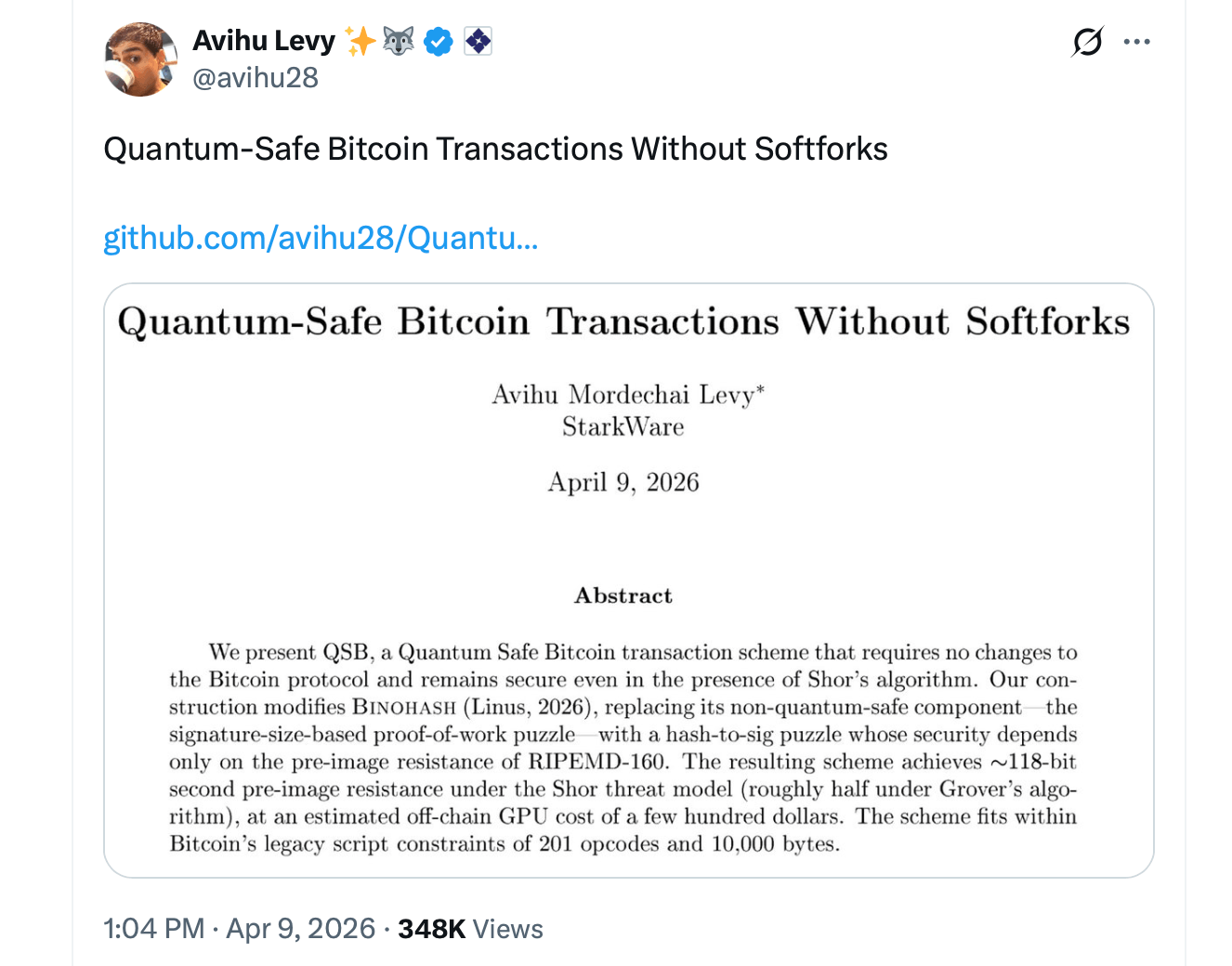 Image source: X.
Image source: X. Levy’s strategy severs that dependency astatine the transaction level. Instead of relying connected elliptic curve hardness, QSB builds information connected the pre-image absorption of RIPEMD-160, a hash relation that quantum computers tin lone onslaught with Grover’s algorithm, which provides a quadratic speedup alternatively than a full break. A 160-bit hash retains astir 80 bits of pre-image absorption against a quantum adversary, leaving a comfy margin.
The operation modifies an earlier strategy called Binohash, developed by Robin Linus, and fixes 2 problems that made Binohash unsafe against quantum attack. The archetypal was a signature-size proof-of-work (PoW) puzzle that depended connected uncovering tiny elliptic curve r-values, thing Shor’s algorithm trivially breaks. The 2nd was an unresolved sighash emblem vulnerability that could let an attacker to reuse a valid puzzle signature crossed antithetic transactions.
Replacing the Signature-Size Puzzle
QSB replaces the signature-size puzzle with what Levy calls a hash-to-sig puzzle. The spender iterates implicit transaction parameters until the RIPEMD-160 hash of a transaction-derived nationalist cardinal produces a valid DER-encoded ECDSA signature. That lawsuit occurs with probability astir 1 successful 70 trillion. Because the puzzle uses a hardcoded SIGHASH_ALL flag, the sighash vulnerability is eliminated arsenic a broadside effect.
The spender past runs 2 digest rounds utilizing a HORS-style Lamport signature structure, selecting subsets of dummy signatures that change the transaction’s sighash via a bequest Script mechanics called FindAndDelete. Each subset produces a antithetic hash output. The subset that yields a valid DER-encoded signature becomes the digest for that round. Revealing the corresponding pre-images successful the witnesser completes the quantum-safe spend.
The recommended configuration, which Levy calls Config A, fits wrong the 201-opcode bounds and achieves astir 118-bit pre-image absorption and 78-bit collision resistance. A quantum attacker moving Grover’s algorithm against this configuration faces astir 2 to the 69th powerfulness enactment for a 2nd pre-image attack. Shor’s algorithm provides nary vantage astatine all, since determination are nary elliptic curve assumptions near to break.
Off-chain computation costs betwixt $75 and $150 successful unreality GPU clip per transaction astatine existent spot pricing. The enactment is embarrassingly parallel and completed successful hours crossed aggregate GPUs successful aboriginal tests. The GPU workplace lone handles nationalist computations, including cardinal betterment and hashing. Private HORS pre-images ne'er permission the spender’s unafraid device.
There are existent limitations. QSB transactions are consensus-valid but non-standard, exceeding default relay policies. They necessitate nonstop submission to a mining excavation that accepts non-standard transactions, specified arsenic done Marathon’s Slipstream service. The strategy does not yet screen Lightning Network channels. Full on-chain assembly and broadcast are inactive pending successful the open-source implementation. Levy describes the strategy arsenic a last-resort measure, not a wide replacement for modular Bitcoin usage.
Starkware co-founder Eli Ben-Sasson publicly endorsed the work, stating Bitcoin tin beryllium quantum-safe immediately. He said:
“THIS IS HUGE. Bitcoin is Quantum-Safe TODAY. Even if a quantum machine appeared, 1 that breaks the accepted Bitcion signatures, it shows a applicable mode to make harmless Bitcoin transactions. WITH NO CHANGE TO BITCOIN PROTOCOL!”
Levy shared the insubstantial and repository connected X and credited Robin Linus for foundational enactment connected Binohash and for a cardinal correction that shaped the last cost-security tradeoff. The assemblage was rather pleased with the achromatic insubstantial arsenic it was shared wide connected societal media. Taproot Wizard Eric Wall wrote connected X:
“Starkware has immoderate of the champion hackers connected the planet. It is beauteous to spot erstwhile hackers usage their powers for good.”
The afloat paper, GPU-accelerated CUDA code, Python pipeline, and implicit Bitcoin Scripts are disposable astatine Levy’s GitHub repository. The quality follows the caller prototype meant to unafraid bitcoin wallets from quantum risk. That specific prototype was created by Lightning Labs CTO Olaoluwa Osuntokun.
What This Means for Everyday Bitcoin Holders
For mundane bitcoin (BTC) holders, the applicable takeaway is straightforward. No quantum computer susceptible of breaking Bitcoin’s cryptography exists today, and astir researchers spot that menace astatine slightest 3 years to a decennary out. But the timepiece starts the infinitesimal a nationalist cardinal appears onchain, which happens each clip a idiosyncratic spends from an address.
Bitcoin sitting successful a wallet that has ne'er made an outgoing transaction carries little exposure. Bitcoin parked astatine a reused oregon already-spent code is simply a antithetic story. When quantum computing reaches the threshold, those exposed nationalist keys go targets. Moving funds earlier that model closes matters much than moving them after.
QSB does not yet vessel wrong immoderate user wallet. Users cannot unfastened a modular wallet contiguous and toggle a quantum-safe setting. What Levy has delivered is the cryptographic impervious that the way exists, built from rules already wrong Bitcoin, costing astir the terms of a level summons successful GPU compute.
The remaining enactment is engineering, adoption, and time. For a idiosyncratic holding BTC, the enactment point is simple: ticker for post-quantum enactment from your wallet provider, debar reusing addresses, and determination funds to a quantum-safe code erstwhile that enactment becomes disposable successful mainstream software. The tools to support that bitcoin are being built close now.

 2 hours ago
2 hours ago








 English (US)
English (US)