Born retired of a hackathon astatine TABCONF 2024, Frostr whitethorn person conscionable solved Nostr’s astir pernicious issue: the inability to reset your password if your backstage cardinal gets compromised.
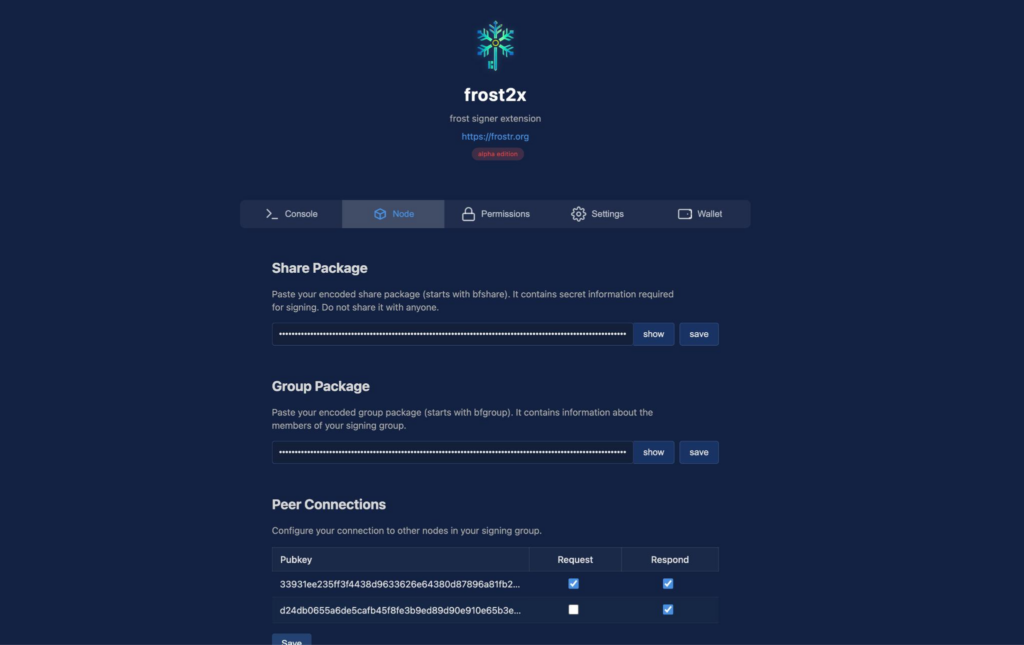
Started successful October of 2024, Frostr conscionable announced the alpha merchandise of Igloo and Forst2x, a desktop and accompanying browser hold cardinal signers for the Nostr ecosystem.
The task was founded by Topher (cmdruid) who made his sanction arsenic a Bitcoin technologist for processing Tapscript — a fashionable room for managing Taproot, Schnorr signatures, and Bitcoin transactions — and Austin (bitcoinplebdev) a Lightning developer for Voltage and laminitis of PlebDevs, a Lightning-powered developer acquisition level with implicit 500 enrolled students.
While resetting a password whitethorn look innocuous oregon similar a elemental UI feature, it’s not that easy. Let maine instrumentality you connected a travel of the complexity of the contented it solves and the magnitude of what is astatine involvement if we neglect to lick this seemingly elemental problem.
The Social Media Revolution
Social media has changed the world. And yet, we find ourselves successful a unusual spot with our integer identities. Who we are online and however we asseverate ownership of our online profiles often depends connected trusted 3rd parties similar Facebook that are excessively large to attraction astir immoderate idiosyncratic lawsuit and fundamentally person the powerfulness to alteration the rules astatine immoderate time, oregon adjacent cancel your relationship altogether.
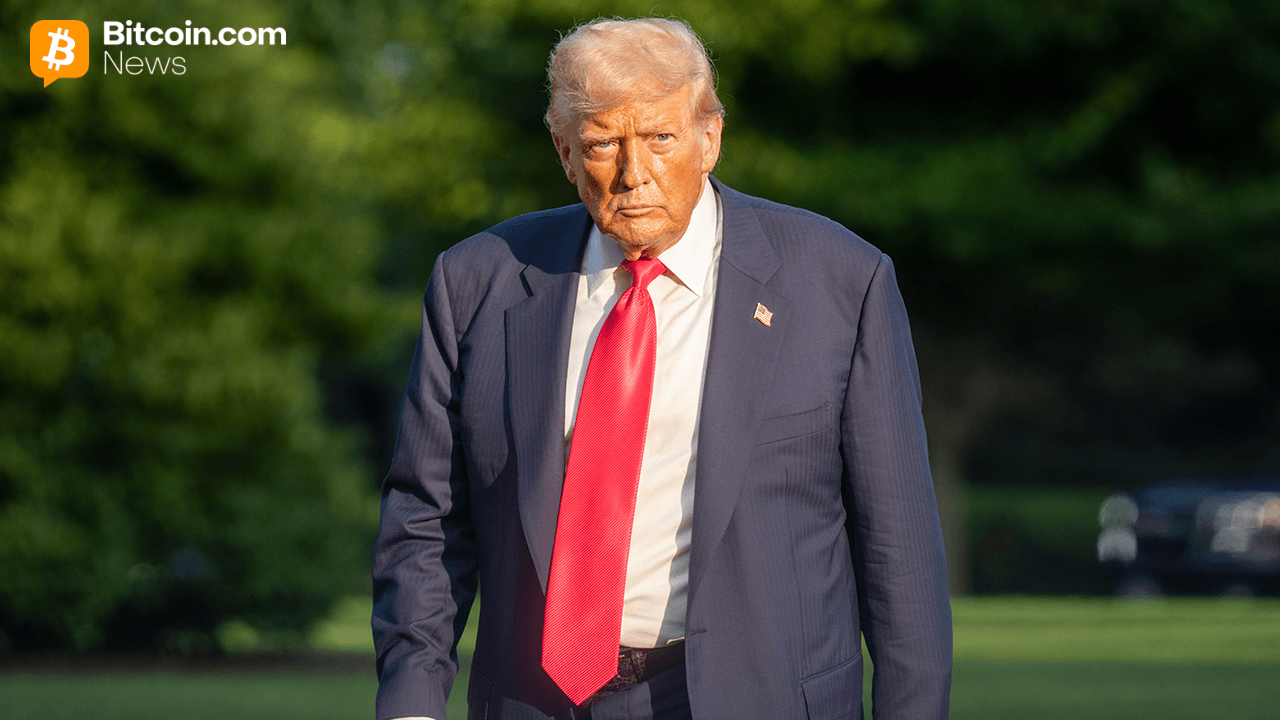
The deplatforming of arguable influencers and adjacent politicians successful caller years service arsenic examples of however this centralized powerfulness tin beryllium wielded. Perhaps the best-known illustration of this is the removal of U.S. President Donald Trump from some Facebook and Twitter soon aft the January 6 riots astatine the U.S. capitol, conscionable days earlier the extremity of his archetypal term.
Still, overmuch of the satellite continues to run connected this integer neo-feudalism structure. It seems there’s a cardinal occupation with the “decentralization” of individuality that is yet to beryllium solved.
Modern-Day Bank Robbery
Identity systems are a captious furniture of society. Whether you are a national of Rome 2,000 years agone oregon of the United States today, doors unfastened and adjacent based connected what ID you hold. Today’s systems, arsenic precocious arsenic they whitethorn seem, trust connected a pre-digital conception of individuality and security: They beryllium connected authenticating your face.
The ID paper itself, whether your driver’s licence oregon passport, helps authorities employees, slope tellers and barroom bouncers each implicit the satellite bash a precise elemental thing: Decide if you look similar the idiosyncratic connected the authoritative card, and past benignant retired if you are allowed entree oregon not.
But the satellite is changing fast. Neither the obscurity of your carnal quality nor the concealed quality of your societal information fig (SSN) are what they were successful the pre-internet world: Many radical person published their afloat names and pictures to Facebook, and a bid of hacks person leaked tons of SSN information to the acheronian web. (For example, the Equifax Data Breach successful 2017, which affected 147.9 cardinal Americans, oregon the National Public Data Breach of 2024 with implicit 200 cardinal Americans compromised.)
In the analog, pre-internet days, erstwhile a robber burst done the doors of their section bank, they would bash truthful to instrumentality the cash, golden and tradable valuables stored successful the vaults.
But that’s nary longer however things work. In the integer age, wealth is nary longer cash. Fiat payments are often reversible, truthful if you hack into a slope and determination wealth to your relationship somehow, not lone tin that beryllium reversed, but you conscionable exposed a nexus to your identity.
Today, the online equivalent of a robber is not looking to bargain cash, golden oregon different valuables, but rather, idiosyncratic individuality data.
That information can, successful turn, beryllium utilized to defraud those aforesaid banks, arsenic good arsenic businesses of each sizes.
Indeed, individuality fraud costs much than each different forms of theft combined, totaling implicit $56 billion successful 2020.
Not lone person galore of these centralized platforms had their information vaults hacked and their contents sold connected the acheronian web for pennies connected the dollar, but AI is improving rapidly and has already passed the Turing trial of representation generation. We are astatine a constituent wherever rogue actors tin make fake selfies holding fake IDs with leaked idiosyncratic information and fool the gatekeepers to your integer wealth.
This menace is apt to incentivize change, and you tin spot the caller efforts by tech companies and authorities institutions to upgrade individuality systems. Take California’s mobile driver’s licence app arsenic an example, mDL — developed successful concern with some Google and Apple — is initially integrated with airports for individuality verification. But the app besides invites developers to integrate it arsenic a signifier of authentication for websites successful general. ID.me takes a akin attack and is already afloat integrated with the IRS, boasting 136 cardinal members.
Many of these apps necessitate look oregon fingerprint authentication, and inquire for progressively analyzable KYC selfies from their users who indispensable clasp up IDs and caller newspapers to beryllium authenticated.
Despite the evident weakness of utilizing your look to authenticate your individuality successful the property of Facebook, tech giants proceed to trust connected biometric data, combining it with wide surveillance tools seen successful the societal recognition people systems being built up in China.
To person a accidental astatine curbing what seems similar destiny successful the integer age, earlier it comes to the West, we request an individuality authentication strategy that is some unafraid and agnostic to biometric data. We request an individuality strategy that does not trust connected our face.
Enter Nostr, a Bitcoin-Era Identity and Social Media Protocol
Born retired of the Bitcoin developer ecosystem, Nostr has rapidly grown into a societal media web successful its ain right.
An abbreviation of “Notes and Other Stuff Transmitted by Relays” — a spot of a mouthful — Nostr empowers users to authenticate themselves into societal media pseudonyms (nyms) and motion their posts with a Bitcoin-style backstage key. As a self-custody strategy that fundamentally democratizes the net distant from its existent structure, it opens up a full caller acceptable of possibilities for societal media.
Proponents of Nostr reason that users tin yet ain their ain information and nary longer request to beryllium connected the foundation oregon benevolence of the Silicon Valley giants erstwhile they determine to determination platforms oregon prime the incorrect governmental party.
Nostr works via a distributed client-server web topology, which allows you to entree contented crossed assorted servers called relays. If 1 goes down oregon starts censoring users unfairly, chances are there’s different model into the Nostr contented provender that volition assistance you entree and let you to people your thoughts.
The imagination of Nostr is to unlock a caller procreation of societal media exertion that does not crook users into products by mining their data, that does not unit biometric authentication, compromising their privacy, and that allows developers to physique successful an unfastened web whose cryptography and specs are already unfastened root and which is natively integrated with Bitcoin, the internet’s money.
Celebrities and users who privation to support their Nostr brands from fake accounts trying to impersonate them tin travel a modular akin to the 1 developed by Keybase, which asked users to publically attest to their a keybase identity with their different societal media accounts, consolidating markers of estimation into 1 cryptographically controlled identity. Though that is not presently a signifier successful Nostr, it is simply a occupation reasonably good solved successful a decentralized mode by Keybase.
However, it’s not each sunshine and rainbows. Pushing individuality ownership to the edges comes with a full caller acceptable of problems that up until present person not truly been solved and which person personally held maine backmost from investing successful gathering up my marque connected Nostr.
No Password Resets
There’s presently nary existent mode to reset your password for a Nostr nym oregon identity. Built connected a elemental nationalist cardinal brace system, if your backstage cardinal gets hacked oregon leaked, your individuality is fundamentally present nether the power of whoever got it. (You some person the secret, truthful nary 1 has exclusive power of it.)
This is simply a immense issue. Although the examples of specified hacks are not excessively common, they are a important deterrent for brands that mightiness see putting superior superior into gathering connected this caller societal web protocol.
This peculiar hazard is made worse by the intended plan of Nostr, which invites galore antithetic interfaces to beryllium created to entree contented of assorted kinds with the aforesaid idiosyncratic identities and means that users springiness their backstage keys to aggregate clients, frankincense multiplying the hazard of compromise.
One furniture of defence that has been built up and go fashionable arsenic a effect is the thought of an outer signer, often a browser hold similar Alby that helps negociate your backstage cardinal arsenic a benignant of password manager, facilitating signing of contented for you connected the assorted Nostr platforms.
While this works good capable contiguous it doesn’t lick the cardinal problem. One mistake and the nym is efficaciously compromised, the worth of that built-up marque oregon estimation not conscionable harmed but perchance exploitable by scammers wearing your individuality to harass your friends oregon customers.
This is akin to the precise communal impersonation scams connected Facebook, Instagram and Twitter, which clone your illustration and DM your known associates with phishing schemes, but adjacent worse. In Nostr specified an onslaught would beryllium done with your identity — not a fake illustration — importantly harming assurance successful the authenticity of each contented for those who are alert of the issue.
The solution should beryllium simple: conscionable make a password reset feature. Right?
Well, it turns retired immoderate precise originative engineering is needed here, due to the fact that password resets are fundamentally lone imaginable by giving up your power implicit your individuality to a 3rd enactment who tin update a cardinal database and springiness you a caller cardinal set.
Until now, that is. Let’s dive into Frostr.
Frost a Breakthrough successful Sovereign Key Management
Recent breakthroughs successful cryptography person opened caller doors for aforesaid custody successful the Bitcoin and cryptocurrency industry. One circumstantial innovation that is rapidly entering the marketplace is Frost, a Schnorr-based cardinal absorption and cardinal rotation strategy that achieves akin functionality arsenic Bitcoin multi-signature addresses and transactions, but without the on-chain transactions costs oregon privateness trade-offs.
Schnorr is simply a signifier of cryptography invented successful the 1990s. A fewer years aft the expiration of its European and U.S. patents, Schnorr started being discussed arsenic a imaginable aboriginal upgrade to Bitcoin, and was yet introduced successful the Taproot brushed fork upgrade of 2020.
That aforesaid twelvemonth Chelsea Komlo and Ian Goldberg published “FROST: Flexible Round-Optimized Schnorr Threshold Signatures”, a method spec that acceptable the instauration for its usage successful the Lightning Network infrastructure arsenic good arsenic caller multi-signature schemes for aforesaid custody known arsenic FROST.
While the cryptography is analyzable and explaining it beyond the scope of this article, it resembles schemes similar Shamir’s concealed sharing. The cryptographic principles progressive let users to make a 24-word effect with Trezor’s hardware wallet, divided up into 3 shares of 12 words each. Any 2 shares combined tin beryllium assembled into the maestro backstage cardinal of the wallet, portion immoderate 1 stock unsocial is insufficient to compromise oregon retrieve entree to the account.
Here’s a two-minute video mentation of FROST by Andrew Poelstra, Head of Research astatine Blockstream:
This aforesaid rule is utilized successful FROST, a strategy which is designed to alteration multi-party, multi-signature wallets, similar those utilized by exchanges, perchance replacing multi-signature Bitcoin scripts, benefiting users with much privateness and little costs.
Frostr extends FROST by integrating it with Nostr’s relay protocol — hence the added “r” successful the name. It besides adapts the exertion to single-user wallets, alternatively than industrial-grade, multi-user schemes, allowing simpler setups and unlocking cardinal rotation (password resets) for idiosyncratic users with azygous cardinal pairs, similar those utilized successful Nostr.
Frostr enables 3 caller features successful particular:
- Threshold cardinal signing, truthful that if 1 cardinal gets compromised, it tin beryllium rotated out, and a caller acceptable of sub keys are generated, which make the Nostr backstage keypair. No request to alteration your Nostr nationalist and backstage keys (nsec). Similar to — for illustration — a 2-of-3 multisignature Bitcoin wallet, wherever if 1 cardinal is mislaid oregon compromised, the different 2 tin beryllium utilized to determination the coins to a caller unchangeable structure, and regain power of 3 caller keys, but off-chain. It’s a magical thing.
- No request for application-layer solutions to Nostr cardinal rotation, lone the cardinal signers similar Alby would person to integrate Frostr; Nostr apps similar Primal oregon Damus would not adjacent cognize that Frostr is being utilized for cardinal rotation by its users.
- Users who already person Nostr accounts, whose nsecs person not been compromised, bash not request to migrate to caller keypairs and identities but simply region their nsecs from existent cardinal signers and commencement utilizing Frostr arsenic a much unafraid cardinal absorption strategy instead.
The result? A large portion of the decentralized societal media puzzle is unlocked: Trustless identities with password resets that bash not beryllium connected centralized gatekeepers for authentication.

 1 year ago
1 year ago







 English (US)
English (US)