An attacker seized power of Wasabi Protocol’s deployer admin cardinal connected Thursday, draining an estimated $4.5 cardinal to $5.5 cardinal from perp vaults and liquidity pools crossed 3 blockchains.
Key Takeaways:
- An attacker drained $4.5M to $5.5M from Wasabi Protocol by compromising the deployer EOA admin cardinal connected April 30, 2026.
- Virtuals Protocol froze borderline deposits instantly aft the breach, though its ain information remained afloat intact.
- Wasabi Protocol has not issued a nationalist statement; users indispensable revoke each approvals crossed Ethereum, Base, and Blast.
DeFi Protocol Wasabi Loses $5M successful Admin Key Hack
The compromised address, 0x5c629f8c0b5368f523c85bfe79d2a8efb64fb0c8, was the sole admin cardinal controlling Wasabi’s Perpmanager contracts. The attacker reportedly utilized it to assistance the ADMIN_ROLE to a malicious helper contract, past executed unauthorized UUPS proxy upgrades connected Wasabivault proxies and the Wasabilongpool earlier sweeping collateral and excavation balances.
Security steadfast Hypernative flagged the incidental with high-severity alerts crossed each 3 chains. Blockaid, Cyvers, and Defimonalerts besides detected the enactment successful existent time. Hypernative confirmed it is not a Wasabi lawsuit but detected the breach independently and pledged a afloat technical analysis.
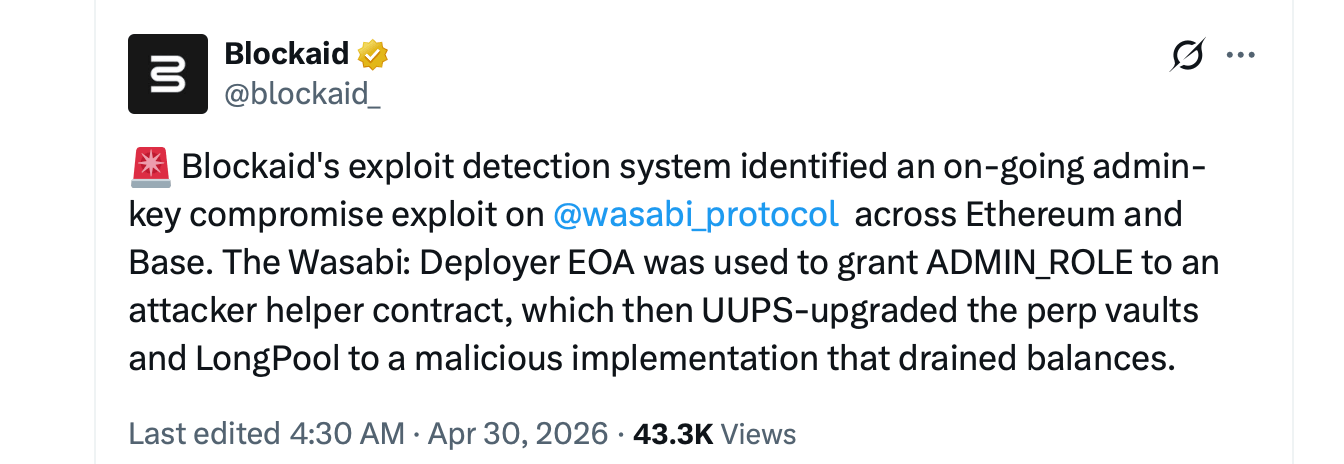 Blockaid informing connected April 30, 2026, astatine 4:30 a.m. ET.
Blockaid informing connected April 30, 2026, astatine 4:30 a.m. ET.The onslaught began astir 07:48 UTC and ran for astir 2 hours. The deployer granted ADMIN_ROLE to attacker-controlled contracts connected Ethereum, Base, and Blast. A malicious declaration past called strategyDeposit() connected 7 to 8 WasabiVault proxies, passing a fake strategy that triggered a drain() relation returning each collateral to the attacker.
The Wasabilongpool connected Ethereum and Base was past upgraded to a malicious implementation that swept remaining balances. Funds were consolidated into ETH, bridged wherever needed, and distributed crossed aggregate addresses. Early reports noted immoderate enactment linked to Tornado Cash.
The largest azygous nonaccomplishment was reportedly 840.9 WETH, worthy much than $1.9 cardinal astatine the clip of the attack. Other drained assets included sUSDC, sREKT, PEPE, MOG, NEIRO, ZYN, and bitcoin, on with Base-chain assets specified arsenic VIRTUAL, AERO, and cbBTC. Wasabi’s full worth locked (TVL) stood astatine astir $8.5 cardinal crossed chains earlier the exploit, according to Defillama data.
This was a key-management failure, not a smart contract vulnerability. No reentrancy oregon logic exploits were involved. The attacker apt obtained the private key done phishing, malware, oregon nonstop theft, past abused the upgradeable proxy architecture to drain funds without triggering accepted information checks.
Virtuals Protocol, which powered borderline deposits done Wasabi, moved rapidly aft the breach was detected. The squad froze each borderline deposits and confirmed its ain information was afloat intact. Trading, withdrawals, and cause operations connected Virtuals continued without disruption. The squad warned users to debar signing immoderate Wasabi-related transactions.
Wasabi Protocol had not issued a nationalist connection oregon incidental station arsenic of the latest disposable data. The protocol has antecedently communicated rapidly during unrelated incidents and holds audits from Zellic and Sherlock, but this onslaught bypassed those protections entirely.
Users with vulnerability are advised to revoke each Wasabi approvals crossed Ethereum, Base, and Blast immediately. Tools similar Revoke.cash, Etherscan, and Basescan tin assistance place progressive approvals. Any remaining LP positions should beryllium withdrawn without delay, and nary Wasabi-related transactions should beryllium signed until the squad confirms cardinal rotation and afloat declaration integrity.
The incidental fits a signifier seen crossed DeFi successful 2026: upgradeable proxy contracts paired with centralized admin keys make a azygous constituent of nonaccomplishment that bypasses adjacent well-audited code. When 1 cardinal controls upgrade permissions crossed aggregate chains, a azygous compromise becomes a protocol-wide event.
The Wasabi breach did not hap successful isolation. April 2026 has seen much than $600 cardinal drained from DeFi protocols crossed astir a twelve confirmed incidents, making it 1 of the worst months connected grounds for the sector. The period opened connected April 1 with attackers draining astir $285 cardinal from Drift Protocol connected Solana successful nether 20 minutes utilizing governance manipulation and oracle abuse.
A 2nd large stroke came astir April 18 erstwhile a Layerzero span exploit deed KelpDAO connected Ethereum, draining astir $292 cardinal successful rsETH and triggering implicit $10 cardinal successful downstream contagion crossed lending platforms, including Aave. Smaller hits landed passim the period connected Silo Finance, Cow Swap, Grinex, Rhea Finance, and Aftermath Finance, among others.
The signifier crossed astir each incidental points distant from code-level bugs and toward admin cardinal compromises, span weaknesses, and upgradeable proxy risks, exposing centralized power points that audits unsocial cannot support against.
The Wasabi concern remains active. Users should show the authoritative @wasabi_protocol relationship and information steadfast feeds for updates.

 1 hour ago
1 hour ago








 English (US)
English (US)