Zetachain paused its mainnet connected April 28 aft a vulnerability successful its GatewayZEVM smart contract was exploited, with information researchers confirming the basal origin wrong hours of the incident.
Key Takeaways:
- Zetachain paused cross-chain transactions connected Tuesday aft an exploit targeting the GatewayZEVM contract’s telephone relation deed interior squad wallets.
- Slowmist identified the basal origin arsenic a missing entree power and input validation successful the telephone function, allowing immoderate idiosyncratic to trigger malicious cross-chain calls without authorization.
- The incidental marks the 2nd large cross-chain exploit successful April 2026, pursuing the KelpDAO hack that triggered the worst DeFi liquidity crunch since 2024.
Slowmist’s Preliminary Analysis
The team pinpointed the GatewayZEVM contract’s telephone relation arsenic being the introduction point. The relation contained nary entree power and nary input validation, a operation that allowed immoderate outer address, without authorization, to trigger malicious cross-chain calls and way them toward arbitrary targets. Wu Blockchain independently confirmed the basal cause soon after.
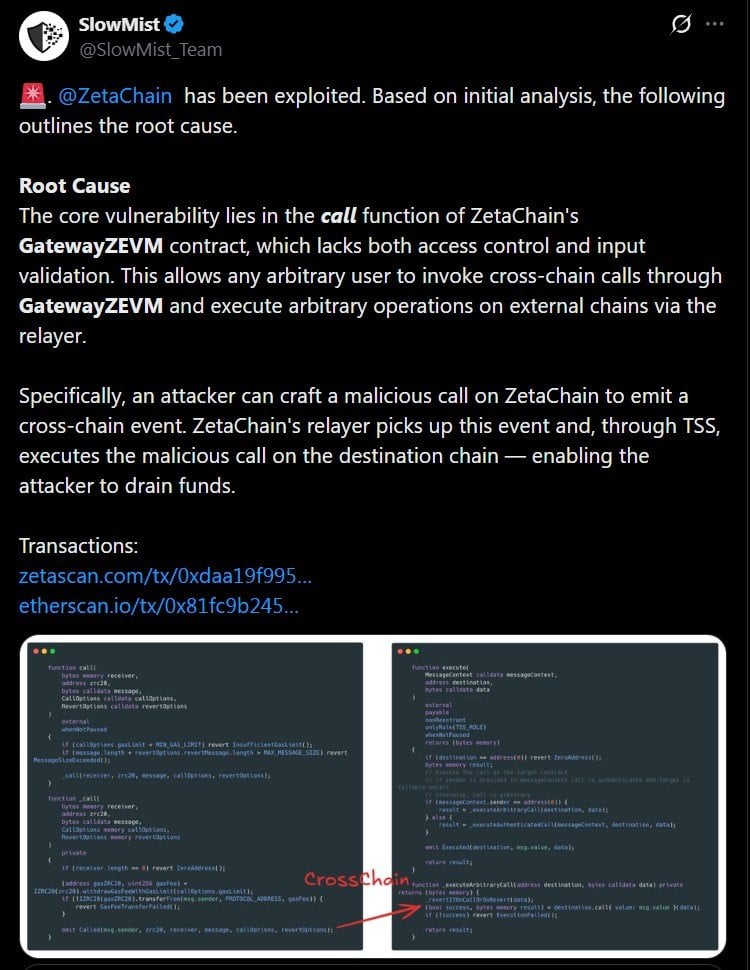 Image source: X
Image source: XZetachain said the exploit affected its ain interior squad wallets (estimated to beryllium worthy $300k), adding that idiosyncratic funds were not straight impacted. The protocol paused cross-chain transactions portion its information squad assessed the afloat scope of the breach. A post-mortem is expected erstwhile the probe concludes.
Moreover, the incidental arrives astatine a hard infinitesimal for cross-chain infrastructure arsenic earlier this month, the KelpDAO exploit triggered a cascade of liquidity withdrawals crossed decentralized finance ( DeFi) protocols, resulting successful the worst crunch successful DeFi since 2024. The Arbitrum Security Council, however, took emergency enactment to frost 30,766 ETH linked to the KelpDAO exploiter.
Access Control Was the Root Issue
Slowmist’s findings person erstwhile again highlighted a recurring signifier successful smart contract exploits wherever missing oregon insufficient entree controls are applied connected functions that grip delicate operations. In Zetachain’s case, the telephone relation successful GatewayZEVM was deployable by immoderate outer code with nary support check, leaving the doorway unfastened for arbitrary inputs to beryllium processed arsenic morganatic cross-chain instructions.
The lack of an input-validation breakstop compounded the hazard because, without checks connected what information the relation receives, attackers tin trade a malicious payload and nonstop it to unintended destinations crossed chains (bypassing immoderate assumed spot boundaries wrong the declaration logic).
Security researchers person consistently flagged insufficient entree controls arsenic 1 of the astir communal and preventable vulnerabilities successful accumulation smart contracts. Whether Zetachain’s GatewayZEVM declaration had undergone a ceremonial third-party information audit anterior to deployment has not been confirmed.

 4 days ago
4 days ago







 English (US)
English (US)